Hundreds of cyber defense teams compared their skills in responding to real-world, simulated attacks.
May 27th officially marked the last day of this year’s International Cyber League. It was a day of intense competition, anticipation, and excitement. Today, we are here to announce the winning teams and give you the inside scoop on the ICL.
Qualifiers – Round 1
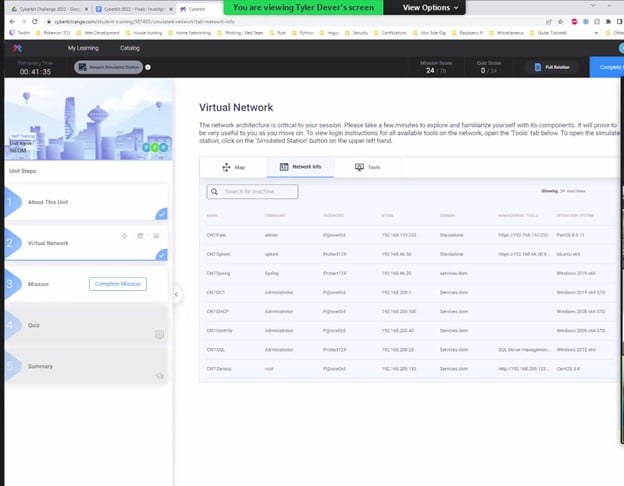
Red Dragon – In this lab, contenders received a report of suspicious behavior on one of the servers in the network. Working individually, each contender had to perform a forensic investigation and locate traces of malware within a small-scale network. They investigated the registry, scheduled tasks, and logs, and performed other steps required to mitigate the malware. Success depended on their ability to understand how the malware operated, use forensic tools, and uncover artifacts.
Brutus – The Brutus lab simulated a security risk that originates within an organization, which is notoriously difficult to detect because it often comes from someone who has legit access to the organization’s network. This particular insider attack came from a disgruntled employee that was stealing information. The Brutus lab tested our contenders’ ability to use cybersecurity tools such as CyberChef, WireShark, and StegHide and required them to investigate the TTPs that insider threats use to perform malicious activity. Understanding TTPS helps investigators understand the way threat actors operate and is therefore crucial to the cyber threat intelligence process.
PowerShell – This exercise focused on a PowerShell exploit, a type of fileless attack, it is one of the most common tactics for evading detection. Fileless attacks are some of the most challenging types of attacks to detect because they are executed through the use of legitimate tools built into a system rather than via code installed on the system by the attacker. A fileless attack is what’s called a low-observable characteristics (LOC) attack. In order to pass the PowerShell exercise, participants had to investigate infected workstations, discover a Keylogging malware and its means of operation, remove the suspicious activity, and restore the network back to its normal state.
The Semi-Finals – Round 2
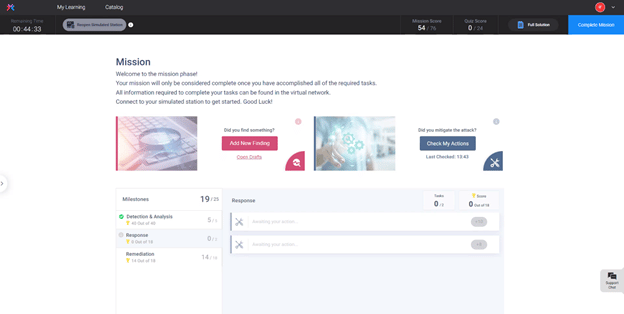
By the time we reached the semi-finals, we were down to just 45 teams. Battling it out in a hyper-realistic environment, which included corporate-grade networks and commercial security tools, contenders now had to work as a team to mitigate a live-fire internal DOS attack.
In this scenario, which uses multiple popular vulnerabilities such as MSHTML and PrintNightmare, the teams received an “AMSI-Detected” alert via Qradar. They then had to use their Qradar, Carbon Black and EPO skills to analyze log sources and uncover attacker activity while also rebuilding the attack flow, reporting their findings, and using Palo Alto Firewall to stop and mitigate the attack.
The Finals – Round 3
And then there were 13 – our finalists, our strongest teams.
Round 3 saw teams competing in another live-fire cyber-attack scenario, but this time it was an ICMP trickster attack. In this type of attack, data is stolen and exfiltrated via ICMP and the webserver. The teams had to double down on their teamwork and skillsets to detect that Splunk had stopped working, use the logs and tools to uncover the exfiltration of NTDS files and mitigate the attack in no more than two hours!
A special shoutout to these teams for passing the semi-finals round and making it to the finals.
Our 13 Finalists
| Company Name | Team Name |
| EmiratesNBD | Team4n6 |
| Baptist Health | Baptist Bandits |
| Availity | TeamBobbyTables |
| Equinix | Established Sheeshion |
| BCC Grupo Cajamar | Blue’s Boys |
| Kantoor Brands | 13MWZ |
| 910th Communication Squadron | Cyber Beasts |
| AT&T | Oxcoffee |
| AT&T | Abducted Death Star |
| National Bank of Canada | Tuk Warriors |
| Deepwatch | Deepwatch |
| RBC | Royal Blue Triangle of Defense |
| FRSecure | Ambush |
But only 4 teams could win… After round 3, the toughest challenge of the ICL, we finally had our winners – the teams that made it through the qualifiers, passed the semi-finals and then completed round 3 with the highest scores and the fastest finish times. Here now are the ICL champions!

Congratulations to all of you for a job well done and this impressive accomplishment!
Thanks to everyone
We also wishto thank all the teams that participated in the ICL this year. Your spirit and enthusiasm were contagious, and all the teams performed admirably, helping make this year’s ICL a huge success. Hats off to all of you!
See you at the ICL in 2023!
Experience the Cyberbit Platform. Request a Demo

